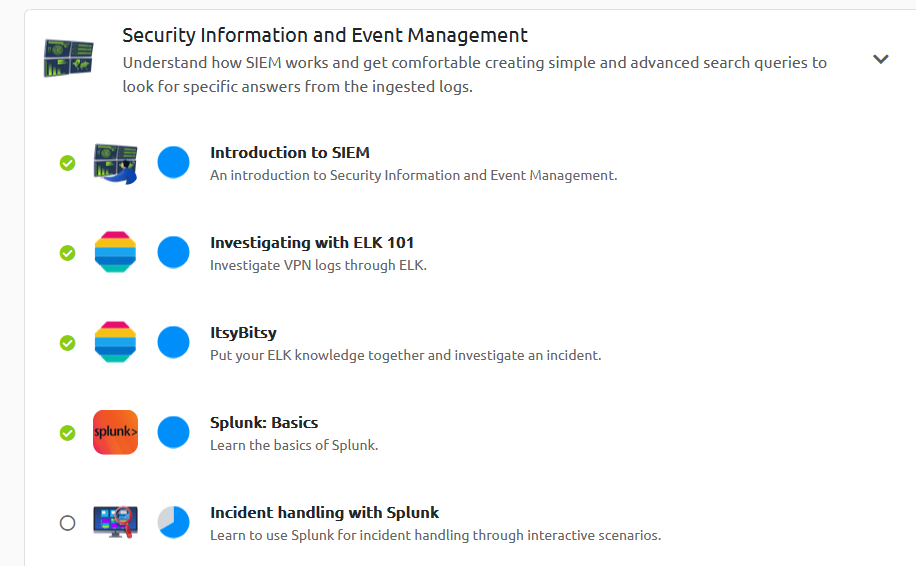
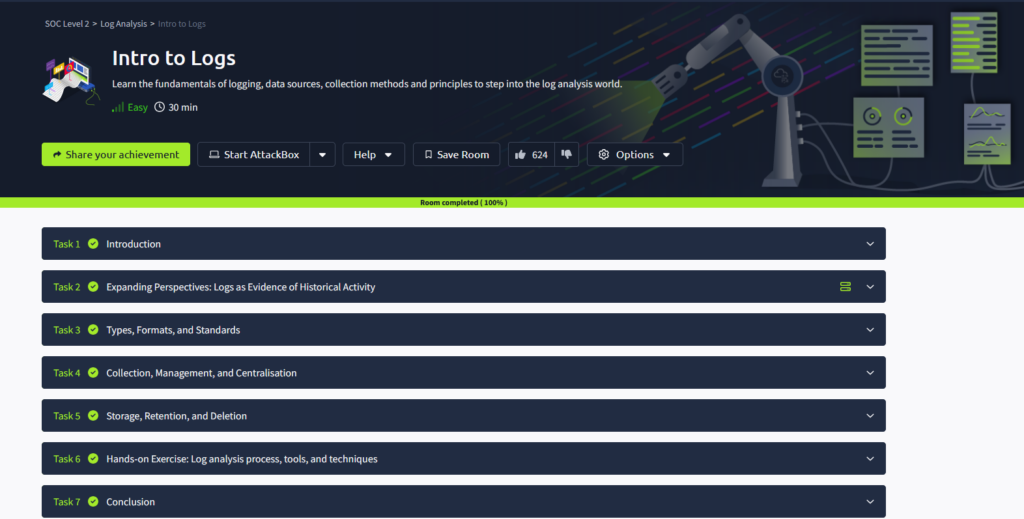
Been messing around on another site similar to TryHackme called Let’s Defend. It was recommended in one of the videos that I was watching for Cyberwox. It seems similar as they allow you to go through and read course material and answer questions to complete modules.
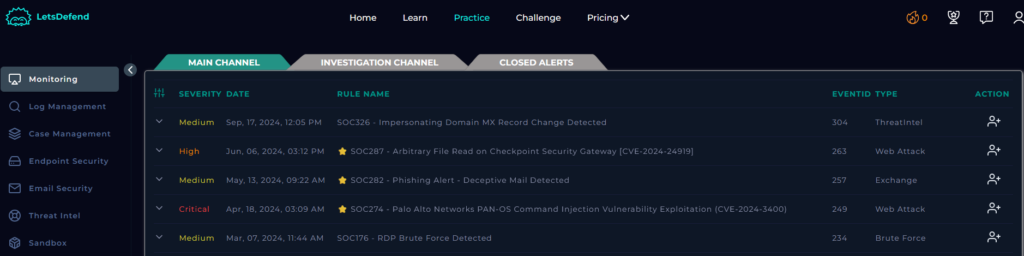
The thing I like about this site is they have a simulated SIEM environment as well with alerts that you can work through.
I had looked at this last year but never got around to creating an account.
Working through the lesson and practicing the SIEM is nice. It simulates a playbook-style setup where you follow the playbook to help answer if the alert is true positive or false positive in some cases. So after going through the answering of questions, you get a score at the end to see how you did. You can even replay some if you want but it doesn’t rescore you.
A good way to practice with SIEMs and alerts you might get in a cybersecurity role.