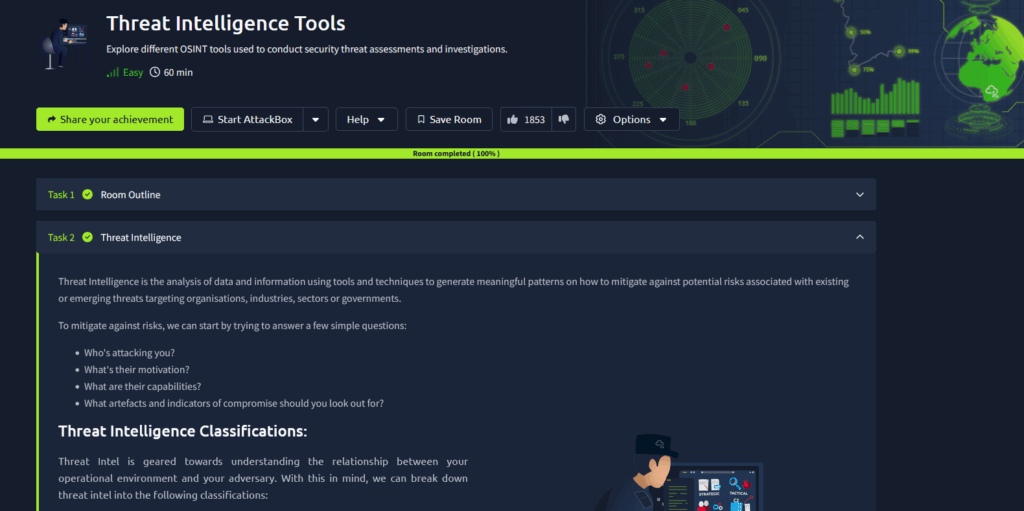
Working through my SOC Level 1 training, I reviewed some different Threat Intelligence tools. This covered some of the Open-Source Intelligence Tools (OSINT) available on the internet, of which there are tons. You would use things like VirusTotal or AbuseIPBD to track malicious files and IP addresses daily in triage alerts to determine whether they are related to a malicious party.