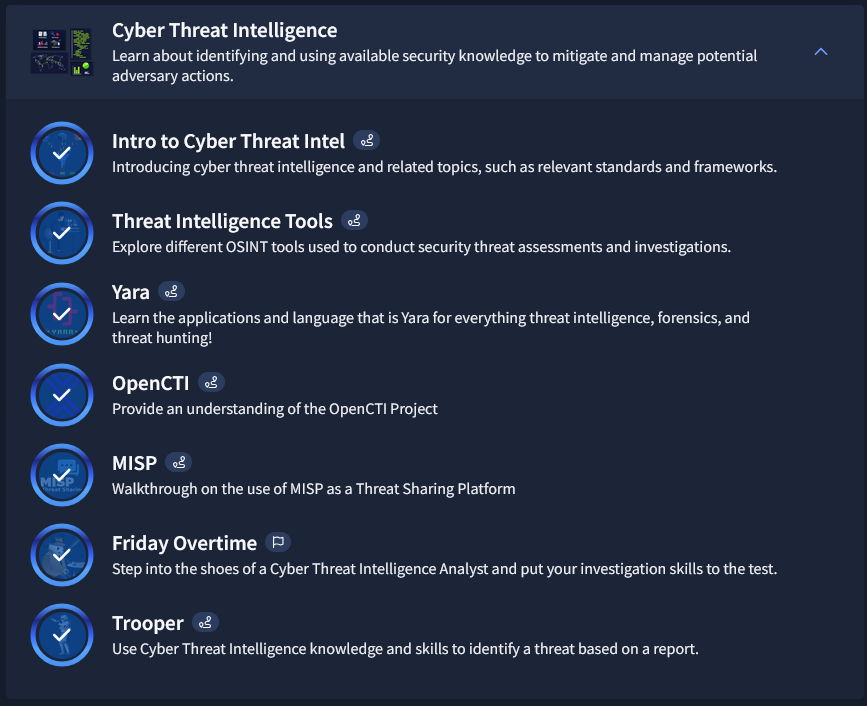
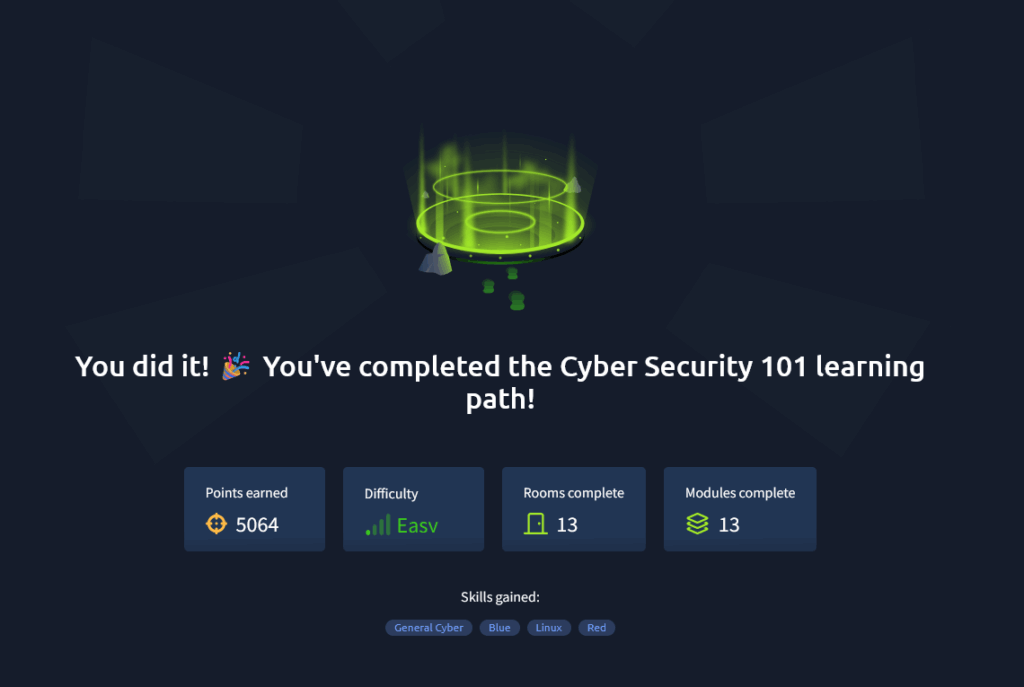
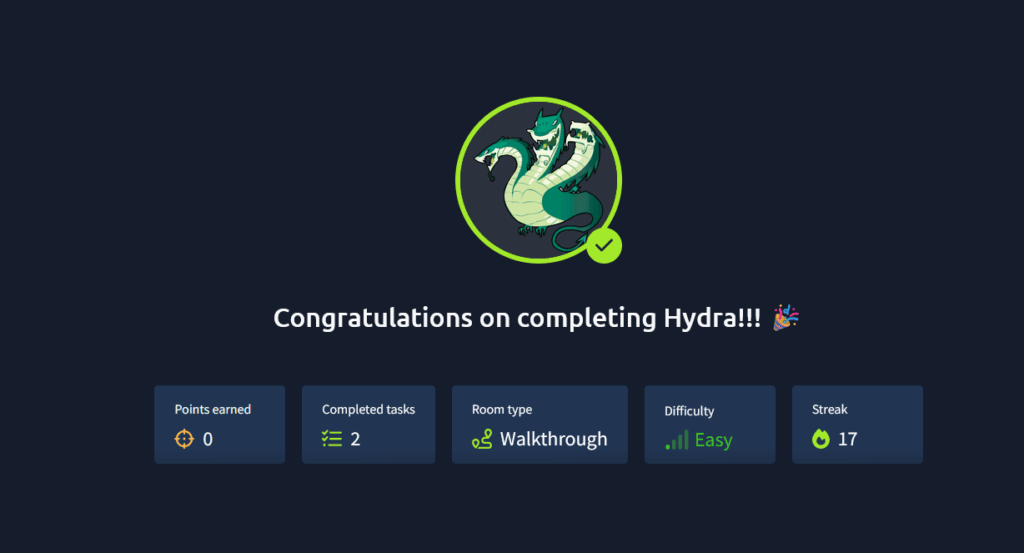
Worked my way through Cyber Threat Intelligence on TryHackMe. Cyber Threat Intelligence combines both paid and open-source materials to help you track active cyber threats and get details on IOCs and APTs. Learning to use tools like Yara to help write and configure rules for both IDS/IPS systems. A good foundation for help with threat hunting and resolution.